How To Read A Vulnerability Scan Report
How To Read A Vulnerability Scan Report - Csv (used in spreadsheets, databases) the html and pdf formats appear very. Web learn more — the linkedin team last updated on aug 17, 2023 a vulnerability scan is a process of identifying and assessing the potential weaknesses and risks in your network, systems, and. A great way to describe a vulnerability in a short, clear way is to. Why should i run a scan report? Testers can also use penetration testing to locate vulnerabilities and determine the severity of a given risk. The open vulnerability assessment system (openvas) started. A vulnerability scanning report is a document which records all findings after a vulnerability scan has taken its course. How to leverage nessus scan reports for better vulnerability. It involves regularly scanning a network to check for vulnerabilities and weaknesses. Web to get a better understanding of the vulnerability assessment process, let’s take a look at the following four stages:
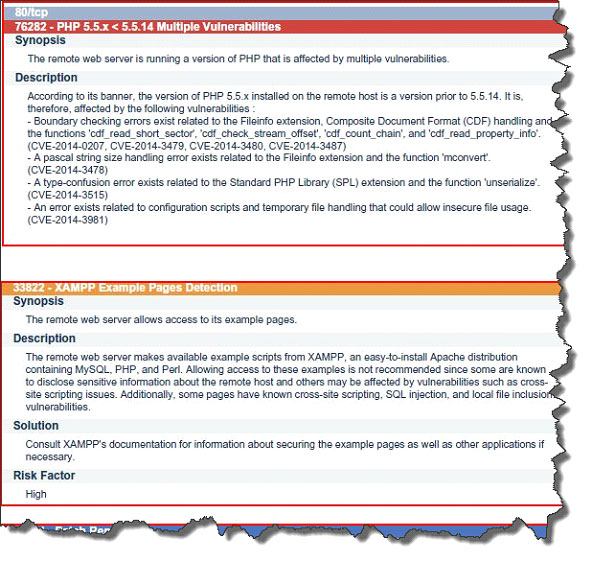
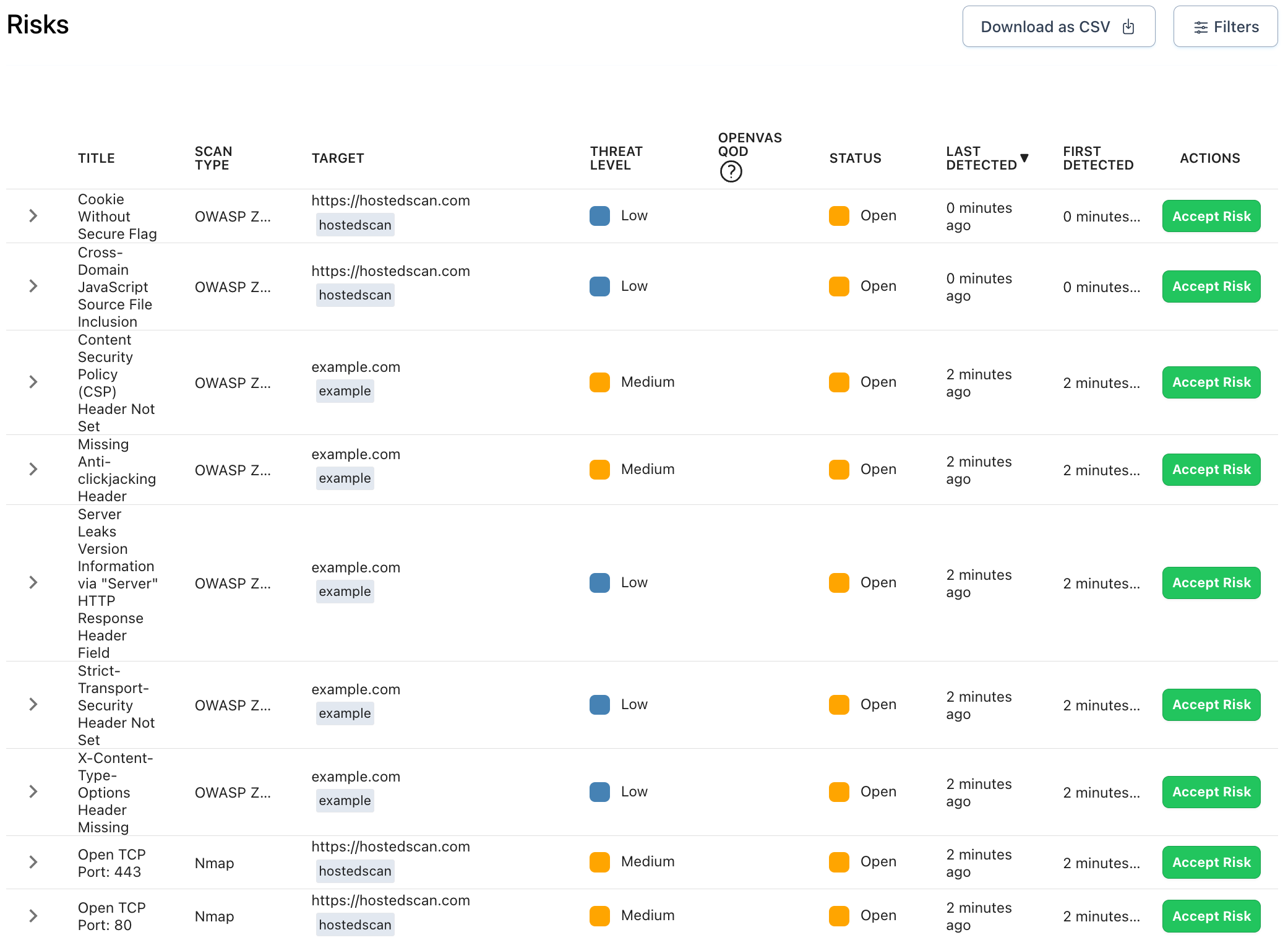
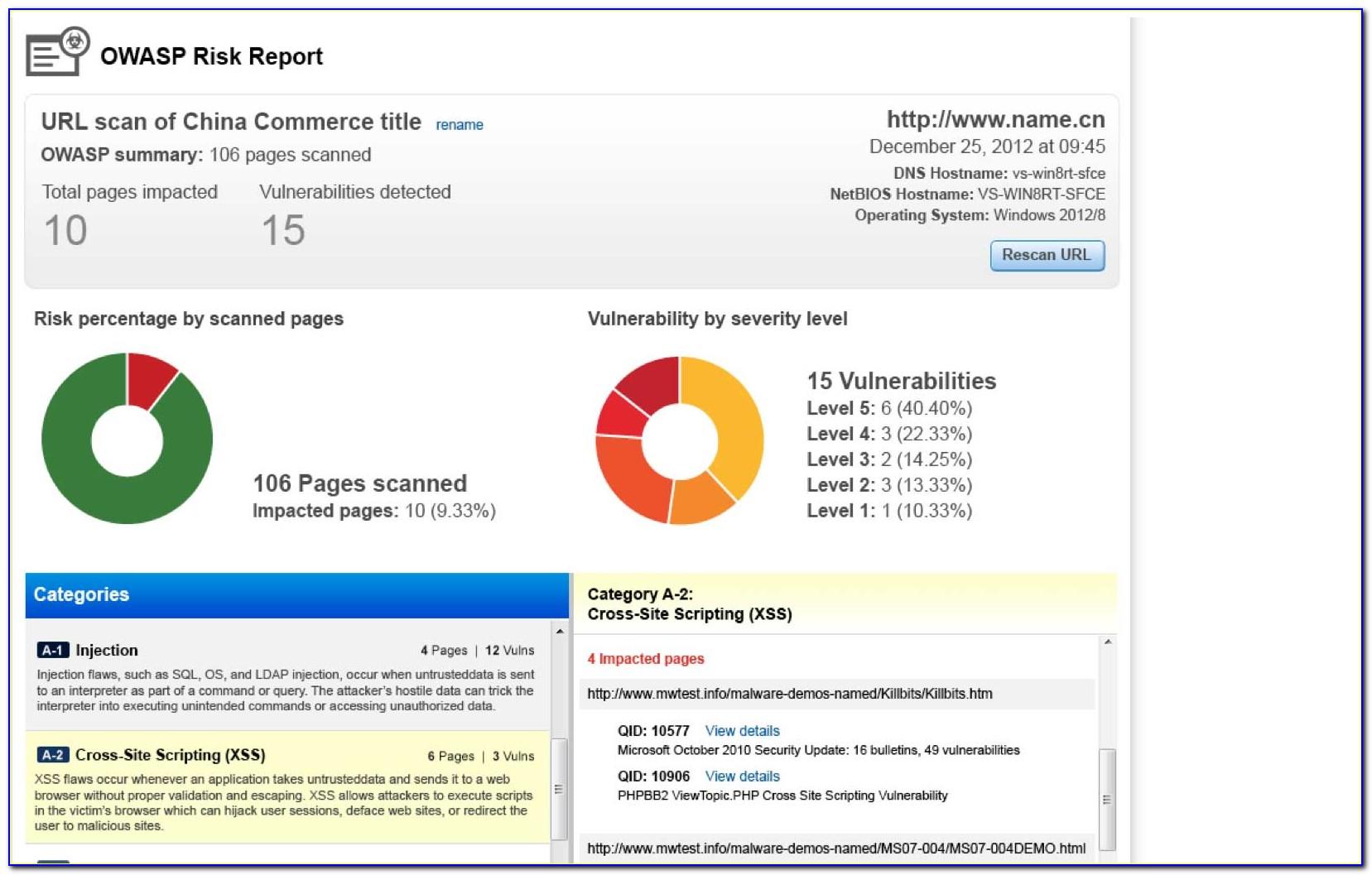
Web an actionable vulnerability scan report identifies vulnerabilities that could pose a threat to your system, tells you the severity of each vulnerability, and provides remediation suggestions. This step includes the identification of assets and definition of risks and significant value for the devices to be used, such as a vulnerability scanner. Web vulnerability scanning, also commonly known as ‘vuln scan,' is an automated process of proactively identifying network, application, and security vulnerabilities. Web a vulnerability description must be short, clear, and direct. A great way to describe a vulnerability in a short, clear way is to. Learn more about it here. Testers can also use penetration testing to locate vulnerabilities and determine the severity of a given risk. Web get started what is a vulnerability scanning report? Web a scan report includes current vulnerability information about hosts in your account (hosts you select at run time). Why should i run a scan report?
Web an actionable vulnerability scan report identifies vulnerabilities that could pose a threat to your system, tells you the severity of each vulnerability, and provides remediation suggestions. Web vulnerability scanning is a process that identifies vulnerabilities in a computer system or network. Web vulnerability scanning, also commonly known as ‘vuln scan,' is an automated process of proactively identifying network, application, and security vulnerabilities. Program owners and clients don’t want to spend much time reading. Why should i run a scan report? Testers can also use penetration testing to locate vulnerabilities and determine the severity of a given risk. The amount of detail included in the report is based on your report template settings. Csv (used in spreadsheets, databases) the html and pdf formats appear very. Web get started what is a vulnerability scanning report? Web a full vulnerability assessment report typically consists of the following elements:
What You Need to Know About Vulnerability Assessments SecureOps
Web learn more — the linkedin team last updated on aug 17, 2023 a vulnerability scan is a process of identifying and assessing the potential weaknesses and risks in your network, systems, and. Web to get a better understanding of the vulnerability assessment process, let’s take a look at the following four stages: Web vulnerability scanning includes automated network and.
Online External Vulnerability Scan HostedScan Security
Learn more about it here. Web an actionable vulnerability scan report identifies vulnerabilities that could pose a threat to your system, tells you the severity of each vulnerability, and provides remediation suggestions. Web to get a better understanding of the vulnerability assessment process, let’s take a look at the following four stages: I demonstrated the scan analysis using excel spreadsheet..
Read Vulnerability Scan Complete SelfAssessment Guide Online by
A nessus vulnerability scan report can be delivered in these formats: Web apart from that, being cautious with what rar files you open and using an antivirus tool that can scan archives would be a good security measure. Web how to read a nessus report. Web get started what is a vulnerability scanning report? Best products cybersecurity companies vulnerability management.
Austins Blog for CIST1001
Web in this video we discussed nessus vulnerability scan analysis, based on popular request by my subscribers. Web turning your nessus scan results into actionable reports helps you dynamically visualize the vulnerability assessment process. Web vulnerability scanning is a process that identifies vulnerabilities in a computer system or network. Testers can also use penetration testing to locate vulnerabilities and determine.
Network Vulnerability Scanning and Why You Need it Now Concensus
The open vulnerability assessment system (openvas) started. A great way to describe a vulnerability in a short, clear way is to. Web vulnerability scanning is a simple concept, but it’s a security measure that can make a world of difference. Web apart from that, being cautious with what rar files you open and using an antivirus tool that can scan.
Web Vulnerability Assessment Report Template Template Resume
The open vulnerability assessment system (openvas) started. Web learn more — the linkedin team last updated on aug 17, 2023 a vulnerability scan is a process of identifying and assessing the potential weaknesses and risks in your network, systems, and. Web a full vulnerability assessment report typically consists of the following elements: Web vulnerability scanning includes automated network and system.
What Is a Vulnerability Scan, and Why Is It Important?
Web turning your nessus scan results into actionable reports helps you dynamically visualize the vulnerability assessment process. The amount of detail included in the report is based on your report template settings. Why should i run a scan report? Testers can also use penetration testing to locate vulnerabilities and determine the severity of a given risk. Program owners and clients.
Vulnerability Management Qualys
Web learn more — the linkedin team last updated on aug 17, 2023 a vulnerability scan is a process of identifying and assessing the potential weaknesses and risks in your network, systems, and. Csv (used in spreadsheets, databases) the html and pdf formats appear very. Web the product security incident response team (psirt) drives adobe's vulnerability disclosure program. The open.
Labor Relations
Web in this video we discussed nessus vulnerability scan analysis, based on popular request by my subscribers. The amount of detail included in the report is based on your report template settings. The severity of vulnerabilities is typically based on the common vulnerability scoring system (cvss) provided by the nist national vulnerability. A nessus vulnerability scan report can be delivered.
Read Vulnerability Assessments Online
I demonstrated the scan analysis using excel spreadsheet. Web a vulnerability description must be short, clear, and direct. The amount of detail included in the report is based on your report template settings. The open vulnerability assessment system (openvas) started. Web learn more — the linkedin team last updated on aug 17, 2023 a vulnerability scan is a process of.
Web In This Video We Discussed Nessus Vulnerability Scan Analysis, Based On Popular Request By My Subscribers.
Web a full vulnerability assessment report typically consists of the following elements: For example, some vulnerability scans are able to identify over 50,000 unique external and/or internal. This step includes the identification of assets and definition of risks and significant value for the devices to be used, such as a vulnerability scanner. Web get started what is a vulnerability scanning report?
Testers Can Also Use Penetration Testing To Locate Vulnerabilities And Determine The Severity Of A Given Risk.
Csv (used in spreadsheets, databases) the html and pdf formats appear very. Web apart from that, being cautious with what rar files you open and using an antivirus tool that can scan archives would be a good security measure. Web a vulnerability description must be short, clear, and direct. Web to get a better understanding of the vulnerability assessment process, let’s take a look at the following four stages:
Executive Summary Assessment Overview Results And Mitigation Recommendations Each Of These Sections.
Why should i run a scan report? Web an actionable vulnerability scan report identifies vulnerabilities that could pose a threat to your system, tells you the severity of each vulnerability, and provides remediation suggestions. Web vulnerability scanning is a simple concept, but it’s a security measure that can make a world of difference. Web vulnerability scanning includes automated network and system scans.
Learn More About It Here.
A vulnerability scanning report is a document which records all findings after a vulnerability scan has taken its course. A great way to describe a vulnerability in a short, clear way is to. Web how to read a nessus report. Web the product security incident response team (psirt) drives adobe's vulnerability disclosure program.